Biometric Web3 Login Surge_ Revolutionizing Digital Security
Biometric Web3 Login Surge: Revolutionizing Digital Security
In the ever-evolving landscape of digital technology, the convergence of biometrics and Web3 is making waves, particularly in the realm of secure online authentication. The surge in biometric Web3 login systems is not just a trend but a transformative shift that promises to redefine digital security. As users seek safer, more convenient ways to access their online accounts, the integration of biometric data into Web3 platforms offers a compelling solution.
The Evolution of Digital Security
Traditionally, digital security relied heavily on passwords—often simple, easily guessed, or forgotten. This method, while convenient, has proven to be less than ideal in the face of increasing cyber threats. The introduction of two-factor authentication (2FA) marked a significant step forward, but it still falls short in providing seamless and robust security. Enter biometrics—the next frontier in digital security.
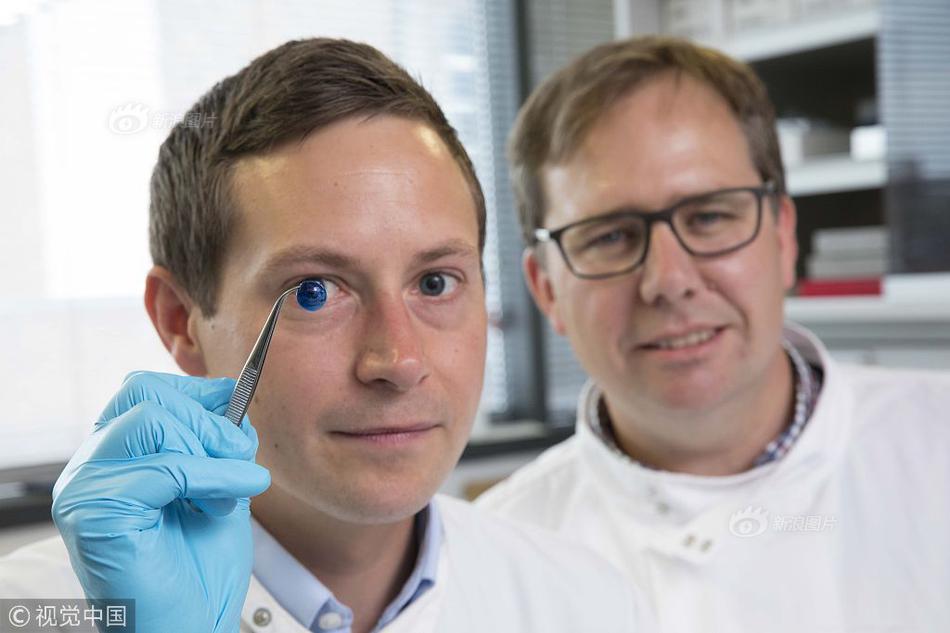
Biometrics leverages unique physical or behavioral characteristics to authenticate users. These can include fingerprints, facial recognition, iris scans, and even voice patterns. When integrated with Web3, a decentralized internet framework built on blockchain technology, biometric login systems offer unparalleled security and convenience.
The Mechanics of Biometric Web3 Login
Biometric Web3 login systems use blockchain’s inherent security features to store and manage biometric data securely. Unlike traditional methods, where sensitive information can be stored on centralized servers vulnerable to breaches, biometric data on a blockchain is encrypted and decentralized, making it significantly harder for malicious actors to access.
How It Works:
Biometric Capture: The first step involves capturing the user’s biometric data using a device. This could be a smartphone camera for facial recognition or a fingerprint scanner.
Data Encryption: The captured data is then encrypted and stored on a blockchain. Blockchain’s distributed ledger ensures that the data is securely stored across multiple nodes, reducing the risk of a single point of failure.
Authentication Request: When a user attempts to log in, the system requests the biometric data. The user provides their biometric input, which is then compared to the stored encrypted data.
Verification: If the biometric data matches the stored data, the system grants access, ensuring that only the rightful owner can log in.
The Benefits of Biometric Web3 Login
Enhanced Security
One of the primary advantages of biometric Web3 login systems is the enhanced security they provide. Biometric data is inherently unique to each individual, making it extremely difficult to replicate or steal. Unlike passwords, which can be forgotten, guessed, or hacked, biometric data is impossible to share or transfer, providing a robust layer of security.
Convenience
Biometric login systems offer unparalleled convenience. Imagine logging into your account without typing a password or even using a security token. This level of convenience is particularly beneficial for users who frequently access their accounts across multiple devices.
Reduced Password Fatigue
The constant need to remember complex passwords, update them regularly, and recover accounts when passwords are forgotten is a significant burden for many users. Biometric login systems alleviate this issue by eliminating the need for passwords altogether, reducing the associated fatigue and frustration.
Privacy
Biometric data, when stored on a blockchain, is encrypted and decentralized. This ensures that sensitive information remains private and is not susceptible to the types of centralized data breaches that have become all too common. Users have greater control over their data, knowing it is stored securely across a distributed network.
Real-World Applications
Biometric Web3 login systems are finding applications across various sectors, each benefiting from the enhanced security and convenience they offer.
Finance
In the financial sector, where the stakes are high, biometric Web3 login systems provide a secure way to manage accounts, conduct transactions, and safeguard sensitive information. This is particularly crucial in preventing fraud and ensuring that only authorized individuals can access financial accounts.
Healthcare
In healthcare, biometric login systems can secure patient records, ensure that medical professionals have access to the right data, and protect patient privacy. This is vital in maintaining the confidentiality of sensitive health information.
E-commerce
For e-commerce platforms, biometric login systems offer a seamless and secure way for customers to shop online. This convenience encourages repeat visits and builds trust, as customers feel their information is well protected.
Challenges and Considerations
While the benefits of biometric Web3 login systems are clear, there are challenges and considerations that need to be addressed to fully realize their potential.
Privacy Concerns
Despite the enhanced security, there are still privacy concerns regarding how biometric data is stored and used. Ensuring that this data is handled responsibly and not misused is paramount. Blockchain’s transparency can help in this regard, as it provides a traceable and immutable record of data usage.
Accessibility
Biometric systems rely on specific hardware, such as cameras or fingerprint scanners, which may not be available on all devices. Ensuring accessibility for all users, including those without advanced technology, is essential.
Ethical Considerations
The use of biometric data raises ethical questions, particularly around consent and data ownership. It is crucial to obtain explicit consent from users before collecting and using their biometric data and to ensure they have control over how their data is used.
The Future of Biometric Web3 Login
As technology continues to advance, the future of biometric Web3 login systems looks promising. Innovations in biometric technology, coupled with the growth of Web3, will likely lead to even more secure and convenient login systems.
Integration with AI
The integration of artificial intelligence (AI) with biometric Web3 login systems can enhance security further. AI can analyze biometric data in real-time, detecting anomalies that may indicate fraudulent activity.
Cross-Platform Compatibility
Future developments will likely focus on ensuring compatibility across various devices and platforms, making biometric login systems accessible to a broader audience.
Enhanced User Control
Efforts will also be directed toward giving users greater control over their biometric data, including the ability to delete or modify their data at any time.
Biometric Web3 Login Surge: Revolutionizing Digital Security
In the concluding part of our exploration into biometric Web3 login systems, we delve deeper into the transformative impact these technologies are having on digital security and user experience. As the digital landscape continues to evolve, biometric Web3 login systems are poised to play a pivotal role in shaping the future of secure online interactions.
The Impact on User Experience
One of the most significant impacts of biometric Web3 login systems is on user experience. Traditional login methods often involve multiple steps, including remembering passwords, navigating to account recovery options, and dealing with security questions. Biometric login systems simplify this process, providing a seamless and intuitive way to access accounts.
User Convenience
Biometric login systems eliminate the need to remember complex passwords or navigate through security questions. Users simply need to present their unique biometric characteristic, whether it’s their fingerprint, face, or voice. This not only saves time but also reduces the frustration associated with password management.
Seamless Multi-Device Access
Biometric Web3 login systems offer seamless access across multiple devices. Whether logging into a banking app on a smartphone, accessing a healthcare portal on a tablet, or managing an e-commerce account on a desktop, the consistent use of biometric data ensures a uniform and hassle-free experience.
Reduced Fraud and Account Takeover
The unique nature of biometric data makes it virtually impossible for attackers to replicate or steal. This significantly reduces the risk of fraud and account takeover, providing users with peace of mind knowing that their accounts are well-protected.
The Role of Blockchain in Biometric Security
Blockchain technology plays a crucial role in the security and management of biometric data within Web3 login systems. By leveraging blockchain’s decentralized and immutable ledger, biometric data can be securely stored and managed in a way that enhances both security and privacy.
Data Integrity
Blockchain ensures that the biometric data stored is accurate and has not been tampered with. This integrity is essential in maintaining the trustworthiness of the login system.
Decentralized Storage
Unlike traditional centralized databases, where data is stored in a single location, blockchain’s decentralized storage spreads the data across multiple nodes. This reduces the risk of a single point of failure and makes it extremely difficult for malicious actors to access or manipulate the data.
Enhanced Privacy
Blockchain’s transparency can also help in enhancing privacy. By providing a traceable record of data usage, blockchain can help ensure that biometric data is used responsibly and in accordance with user consent.
Adoption and Integration
The adoption of biometric Web3 login systems is growing, driven by both technological advancements and user demand for more secure and convenient login methods. Several companies and platforms are already integrating these systems, and the trend is expected to continue.
Enterprise Adoption
In the enterprise sector, biometric Web3 login systems are being adopted to secure sensitive information and streamline access for employees. This includes secure access to corporate networks, safeguarding confidential documents, and ensuring that only authorized personnel can access critical systems.
Consumer Adoption
Consumer-facing platforms, from banking to e-commerce, are increasingly adopting biometric login systems to enhance security and convenience. Users benefit from faster and more secure access to their accounts, while platforms can reduce the burden of password management.
Future Trends and Innovations
The future of biometric Web3 login systems is bright, with several trends andinnovations on the horizon that promise to further enhance their capabilities and integration into everyday digital life.
Multi-Factor Biometric Authentication
One of the future trends in biometric Web3 login systems is the development of multi-factor biometric authentication. This approach combines biometric data with other forms of authentication, such as one-time passwords (OTPs) or security tokens, to provide an additional layer of security. This ensures that even if one factor is compromised, the account remains secure.
Enhanced Security
Multi-factor authentication significantly enhances security by requiring multiple forms of verification. For instance, a user might be required to scan their fingerprint and enter a one-time password sent to their mobile device. This dual approach makes it extremely difficult for attackers to gain unauthorized access.
User Convenience
Despite the added security, multi-factor biometric authentication can still offer a convenient user experience. Many modern devices support seamless integration of multiple authentication methods, ensuring that users do not need to perform cumbersome steps to access their accounts.
Integration with IoT Devices
The Internet of Things (IoT) is another area where biometric Web3 login systems are making significant inroads. As more devices become connected, the need for secure and convenient access methods grows. Biometric login systems can provide a secure way to access IoT devices, from smart home systems to wearable technology.
Secure Access
Biometric login systems offer a secure way to access IoT devices without the need for passwords. For example, a smart home system can be accessed by simply scanning a user’s fingerprint, ensuring that only authorized individuals can control the home’s security and climate settings.
Enhanced User Experience
The integration of biometric login systems with IoT devices enhances the user experience by providing seamless and secure access. This is particularly beneficial for users who rely on multiple IoT devices to manage their daily routines, offering a more cohesive and secure environment.
Advanced Biometric Technologies
The development of advanced biometric technologies is also a key trend in the future of biometric Web3 login systems. Innovations in areas such as liveness detection and advanced pattern recognition are set to further improve the accuracy and reliability of biometric authentication.
Liveness Detection
Liveness detection technology can distinguish between real biometric data and fake replicas. For instance, facial recognition systems can now detect whether the face being scanned is a real, live person and not a photograph or mask. This significantly reduces the risk of spoofing attacks.
Advanced Pattern Recognition
Advancements in pattern recognition algorithms enable more precise and reliable biometric authentication. For example, advanced fingerprint recognition systems can now capture and analyze minutiae points with higher accuracy, ensuring that the authentication process is both secure and efficient.
Regulatory and Ethical Considerations
As biometric Web3 login systems become more prevalent, regulatory and ethical considerations will play a crucial role in their development and deployment. Ensuring compliance with data protection regulations and addressing ethical concerns around biometric data usage are essential.
Data Protection Regulations
Compliance with data protection regulations, such as the General Data Protection Regulation (GDPR) in Europe, is crucial for the responsible use of biometric data. These regulations mandate the protection of personal data and the right to privacy, which are fundamental to the secure and ethical use of biometric login systems.
Ethical Use of Biometric Data
Ethical considerations around the use of biometric data include issues such as consent, data ownership, and the potential for misuse. Ensuring that users provide explicit consent for the collection and use of their biometric data, and giving them control over how their data is used, is essential for maintaining trust and ethical standards.
The Role of User Education
User education will play a vital role in the successful adoption of biometric Web3 login systems. As these technologies become more integrated into daily life, educating users about their benefits and the importance of security will be crucial.
Awareness of Benefits
Educating users about the benefits of biometric login systems, such as enhanced security and convenience, will help to build trust and encourage adoption. Understanding how biometric data is securely stored and managed on a blockchain will also reassure users about the safety of their information.
Security Best Practices
Providing users with information on security best practices, such as avoiding sharing biometric data with third parties and ensuring that their devices are secure, will help to mitigate risks. Educating users on the importance of regularly updating their biometric data can also enhance security.
Conclusion
Biometric Web3 login systems are revolutionizing digital security, offering enhanced security, convenience, and privacy. As technology continues to advance, these systems will play an increasingly important role in shaping the future of secure online interactions. By addressing challenges related to privacy, accessibility, and ethical considerations, and by fostering user education and awareness, biometric Web3 login systems can provide a secure and seamless experience for users across various sectors and applications.
The future of biometric Web3 login systems is bright, with the potential to transform the way we access and secure our digital lives. As we move forward, it is essential to continue innovating, educating, and responsibly managing biometric data to ensure a secure and user-friendly digital future.
The Mechanics and Promise of Hardware Wallets
Hardware wallets, often hailed as the most secure way to store cryptocurrencies, operate by keeping private keys offline, away from the prying eyes of potential hackers. These devices, such as Ledger Nano S or Trezor, generate and store private keys locally on the device and only sign transactions without exposing the keys to the internet. The promise of these devices is a fortress of security, offering a safer haven for digital assets than traditional online wallets.
The Role of Firmware
At the heart of a hardware wallet lies its firmware—a set of instructions that define its operations. Firmware controls every aspect of the device, from user interface interactions to cryptographic processes. Given its central role, any flaw in the firmware can potentially turn this supposed fortress into a vulnerable gateway.
Types of Firmware Vulnerabilities
Firmware vulnerabilities can stem from various sources:
Code Vulnerabilities: These are flaws within the firmware’s code. They can be anything from buffer overflows to incorrect validation checks that could allow an attacker to execute arbitrary code or manipulate the device’s behavior.
Supply Chain Attacks: Just like any other technology, hardware wallets are susceptible to supply chain attacks. If a third-party component is compromised, it could introduce vulnerabilities that affect the entire device.
Reverse Engineering: Skilled hackers might reverse engineer the firmware to understand its inner workings. This can lead to the discovery of hidden vulnerabilities that could be exploited to gain unauthorized access to the wallet.
Physical Attacks: Hardware wallets can be subjected to physical attacks where attackers attempt to manipulate the device's hardware or force it to reveal its secrets. This can include techniques like Power Analysis, where the electrical consumption patterns during cryptographic operations are analyzed to deduce private information.
The Silent Threat of Firmware Updates
Firmware updates are intended to patch vulnerabilities and introduce new features, but they can also introduce new risks. If an update is not properly vetted or if the update process itself is flawed, it can open up new attack vectors. Users must ensure that updates come from official channels and be wary of phishing attempts that mimic legitimate firmware update notifications.
Case Studies in Firmware Vulnerabilities
To understand the real-world impact of firmware vulnerabilities, let's look at some notable incidents:
Ledger’s 2018 Incident: In 2018, Ledger experienced a phishing attack targeting their customers. Hackers tricked users into downloading a malicious application that, when run, extracted the seed phrases from the Ledger device. This incident highlighted the importance of not just device security but also user education and secure communication channels.
Trezor’s 2020 Firmware Update: In 2020, Trezor faced scrutiny when a poorly managed firmware update led to a temporary loss of access for many users. While this wasn’t a vulnerability in the traditional sense, it demonstrated the risks that can arise from flawed update processes.
The Path Forward: Enhancing Firmware Security
To mitigate the risks associated with firmware vulnerabilities, several strategies can be adopted:
Rigorous Code Review: Employing a team of experts to perform exhaustive code reviews can help identify and rectify potential vulnerabilities before they become exploitable.
Open Source Audits: Making firmware open source allows the broader cybersecurity community to audit the code for vulnerabilities, fostering a collaborative approach to security.
Secure Development Practices: Following secure coding standards and incorporating security best practices during development can significantly reduce the likelihood of vulnerabilities.
User Awareness: Educating users about the risks and safe practices related to firmware updates and device security is crucial. Users should be encouraged to verify the source of any updates and remain vigilant against phishing attempts.
Conclusion
The security of hardware wallets hinges not only on their physical design but also on the integrity of their firmware. While these devices offer a robust method for securing digital assets, they are not immune to vulnerabilities. By understanding the types of threats and adopting best practices in development and user education, we can enhance the security of these essential tools in the cryptocurrency ecosystem. In the next part, we will explore specific case studies in more depth and discuss advanced techniques for identifying and mitigating firmware vulnerabilities.
Advanced Techniques and Future Trends in Hardware Wallet Firmware Security
In-Depth Case Studies
Ledger’s 2018 Phishing Attack
The 2018 phishing incident underscores the importance of secure communication channels and user education. Ledger's response included not only patching the vulnerabilities but also launching an extensive user awareness campaign. They highlighted the importance of verifying email sources and avoiding unsolicited software downloads. This incident serves as a stark reminder that while hardware wallets offer robust security, the human element remains a critical vulnerability.
Trezor’s Firmware Update Mishap
The 2020 firmware update fiasco for Trezor highlighted the risks of flawed update processes. In this case, Trezor had to issue a second update to rectify issues caused by the first. This incident emphasizes the need for thorough testing and validation before deploying updates. It also demonstrates the importance of transparent communication with users during such processes.
Advanced Techniques for Identifying Vulnerabilities
Static and Dynamic Analysis
Security researchers employ static and dynamic analysis techniques to uncover firmware vulnerabilities:
Static Analysis: This involves examining the firmware code without executing it. Tools can be used to identify potential vulnerabilities such as buffer overflows, incorrect pointer usage, or other code flaws.
Dynamic Analysis: This involves running the firmware in a controlled environment and monitoring its behavior. Techniques like fuzz testing can help discover vulnerabilities by inputting large amounts of random data to the firmware and observing any crashes or unexpected behaviors.
Hardware-Level Attacks
Differential Power Analysis (DPA): This technique analyzes the power consumption patterns of a device to deduce cryptographic secrets. By measuring the electrical activity during cryptographic operations, an attacker can potentially recover private keys. Hardware wallets must implement countermeasures like power balancing to mitigate DPA attacks.
Simple Power Analysis (SPA): Similar to DPA, SPA measures the power consumption of a device during simple operations like key presses. By analyzing these patterns, an attacker might gain insights into the device's internal state, which can be used to derive sensitive information.
Advanced Encryption and Secure Boot
Post-Quantum Cryptography: As quantum computers become more prevalent, traditional encryption methods are at risk. Adopting post-quantum cryptographic algorithms can help future-proof hardware wallets against quantum attacks.
Secure Boot: Implementing secure boot mechanisms ensures that only verified firmware can run on the device. This prevents malicious code from being executed during the boot process, adding an additional layer of security.
Future Trends in Firmware Security
Blockchain Integration
Integrating blockchain protocols directly into the firmware can enhance security. By leveraging blockchain’s decentralized nature, hardware wallets can provide more resilient security mechanisms against attacks.
User-Centric Security Measures
Biometric Authentication: Incorporating biometric authentication methods like fingerprint scanning or facial recognition can provide an additional layer of security. Users can benefit from a more seamless experience while maintaining high security standards.
Multi-Signature Schemes: Implementing multi-signature schemes where multiple keys are required to authorize a transaction can significantly enhance security. Even if one key is compromised, unauthorized access remains unattainable without the other required keys.
Real-Time Threat Detection
Machine Learning: Employing machine learning algorithms to monitor the device’s behavior in real-time can help detect anomalies indicative of a potential attack. These algorithms can learn normal patterns of operation and flag any deviations that might suggest a security breach.
Conclusion
The security of hardware wallets is a multi-faceted challenge that extends beyond the physical device to encompass the integrity of its firmware. By employing rigorous security practices, adopting advanced techniques for vulnerability identification, and embracing future trends in security, we can safeguard these critical tools against the ever-evolving landscape of cyber threats. The journey towards ultimate security is ongoing, and it requires a concerted effort from developers, security researchers, and users alike. As we move forward, staying vigilant and proactive will be key to maintaining the trust and security of our digital assets.
This concludes our exploration into the intricate and ever-evolving world of hardware wallet firmware vulnerabilities. The landscape is complex, but with the right strategies and a commitment to security, we can ensure that our digital assets remain protected.
Affiliate Marketing for Web3 Projects_ Building a Referral Network
Crypto Opportunities Everywhere Unlocking a New Era of Possibilities